You’re likely reading this email link at some point. Perhaps you’re a marketer trying to understand what happens when your carefully crafted campaign lands in an inbox, or maybe you’re a curious individual who’s noticed those slightly unusual URLs. Whatever your motivation, you’ve stumbled upon a fascinating, often unseen, infrastructure: email tracking links and redirects. They are the silent conductors of digital communication, orchestrating data collection and directing your digital journey. This article will delve into their mechanics, demystifying their operation and the implications they carry.
At their core, email tracking links are designed for one primary purpose: to gather information about user interaction with an email. They are not merely simple hyperlinks leading to a destination. Instead, they are sophisticated intermediaries, meticulously crafted to record your actions before, and sometimes after, you reach your intended digital real estate.
Identifying an Email Tracking Link
You might not always recognize them at first glance. While some tracking links are embedded within call-to-action buttons that visually appear to lead directly to a website, others are subtly woven into standard text links or even image links. The key differentiator is not always its appearance but its underlying function.
The Hidden Parameters
The most definitive characteristic of a tracking link is the presence of appended parameters. These are the snippets of text and numbers that follow a question mark (?) in a URL. For instance, a standard link might be https://www.example.com/page. A tracked link, however, could look like https://www.example.com/page?utm_source=newsletter&utm_medium=email&utm_campaign=spring_sale&id=12345. These utm_ parameters, commonly used by platforms like Google Analytics, are just one type of tracking data. Other parameters can be vendor-specific, containing identifiers that are unique to the email platform or the individual recipient.
The Purpose of Unique Identifiers
Each tracking link often contains a unique identifier. This could be a randomly generated string, a user ID, or a combination of both. This identifier is crucial for discerning individual user behavior from aggregate data. Without it, a marketer would only know that someone clicked a link, not which specific recipient made the click. This granular detail allows for personalized follow-ups, segmentation of audiences based on engagement, and a deeper understanding of what resonates with individuals.
The Silent Data Collectors
The information gathered by these links goes beyond a simple click count. They can provide valuable insights into various aspects of user engagement, helping to refine marketing strategies and improve user experience.
Click Attribution
The most basic data point is the click itself. When you click a tracked link, the tracking mechanism registers this event. This attribution is fundamental for understanding which email campaigns, subject lines, or calls to action are most effective in driving traffic. By knowing which links were clicked and how many times, marketers can allocate resources more efficiently and focus on strategies that yield the best results.
Open Tracking (Implicitly Linked)
While not directly a function of the link itself, open tracking technology is often implemented in conjunction with link tracking. When you open an email containing a tiny, invisible image (a web beacon or pixel tag), the server hosting that image is notified. This registration is often a prerequisite for the tracking link to become active. In essence, the open is registered, and then subsequent clicks are meticulously logged. This provides a more complete picture, allowing marketers to understand not only who received the email but also who engaged with it to the point of opening.
Engagement Metrics
Beyond a simple click, tracking links can sometimes capture more nuanced engagement. This might include the time spent on the landing page after the click, the number of subsequent pages visited, or even scroll depth. While this data is often collected by the destination website’s analytics, the initial click through the tracking link serves as the entry point for this data collection process.
The Redirect: A Necessary Detour
Email tracking links rarely point directly to the final destination. Instead, they are almost always routed through one or more redirect servers. This detour is where the magic – or perhaps the surveillance – happens, as the system records your action before sending you on your way.
The Role of the Redirect Server
Imagine a postal service that requires you to first drop your letter at a sorting facility before it’s sent to its final address. The redirect server plays a similar role in the digital world. It’s an intermediary server that receives your initial request and performs specific actions before forwarding you to the actual URL.
The Tracking Pixel Connection
The redirect server is intrinsically linked to the tracking pixel or web beacon embedded in the email. When you click a tracked link, your browser is directed to a URL on the redirect server. This action, in turn, triggers a request to the tracking pixel’s server, registering your interaction. This initial interaction is crucial for pinging the tracking server and logging the event.
Capturing Your Digital Fingerprint
As your request hits the redirect server, it has an opportunity to capture a wealth of information. This includes your IP address, the browser you are using, your operating system, and the timestamp of your click. This data, when combined with the unique identifier associated with the tracking link, begins to build a profile of your online behavior.
The Seamless Transition (or Not So Seamless)
For the end-user, the redirection process is usually designed to be as seamless as possible. You click a link, and within a fraction of a second, you arrive at your intended destination. However, occasionally, the intermediaries involved can cause delays or introduce other inconsistencies.
The Illusion of Directness
The primary objective of the redirect mechanism is to create the illusion that you clicked directly on the original link. The redirect server swiftly processes your request and forwards you to the final URL, often before your browser has a chance to fully render the redirect server’s domain. This sophisticated routing ensures that the tracking process remains largely invisible to the casual observer.
Potential for Delays and Errors
While generally efficient, the chain of redirects can sometimes introduce latency. If any of the intermediate servers are slow to respond or experience technical difficulties, you might notice a slight delay before your intended page loads. In rare cases, broken redirects can lead to error pages, interrupting your browsing experience. This underscores the complex network of servers and systems that are involved in even the simplest-seeming click.
How the Data is Processed and Stored

The information collected by tracking links and redirects doesn’t simply vanish into the digital ether. It’s meticulously organized, processed, and stored, forming the basis of valuable analytics and insights.
The Backend Infrastructure
Behind every successful email tracking operation lies a robust backend infrastructure. This involves sophisticated servers, databases, and software designed to handle the influx of data from countless clicks.
Databases and Data Warehousing
The raw data from each click – the identifier, timestamp, IP address, etc. – is fed into databases. For large-scale operations, this data is often consolidated into data warehouses, where it can be queried and analyzed efficiently. These databases are the repositories of your digital footprint, meticulously organized for retrieval.
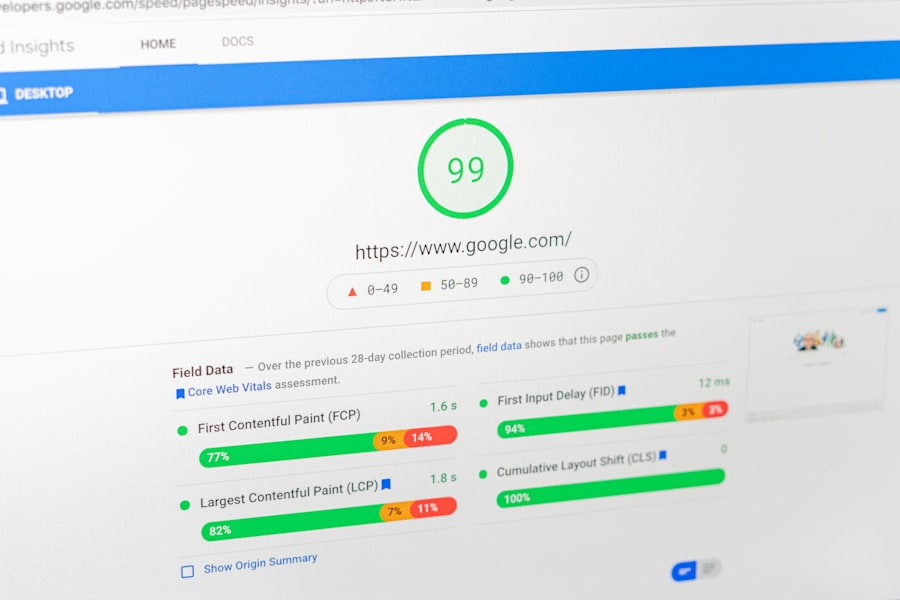
Analytics Platforms and Reporting Tools
Specialized analytics platforms, such as Google Analytics, Adobe Analytics, or proprietary marketing automation tools, are then used to interpret this raw data. These platforms transform the collected information into comprehensible metrics and reports. You’ll see summaries of click-through rates, conversion rates, engagement times, and audience demographics, all derived from the initial click data.
The Transformation of Raw Data into Actionable Insights
The true value of tracking lies not just in collecting data but in transforming it into meaningful information that can drive decision-making.
Segmentation and Personalization
By analyzing which links individuals click, marketers can segment their audience based on their interests and engagement levels. This allows for more targeted and personalized communication in the future. For example, if you repeatedly click on links related to a specific product category, you’re likely to receive more content focused on that area.
Campaign Optimization
Reports generated from tracking data provide invaluable feedback on the performance of email campaigns. Marketers can identify which subject lines lead to higher open rates, which calls to action drive more clicks, and which content resonates most with their audience. This data-driven approach allows for continuous refinement and optimization of future campaigns.
A/B Testing and Performance Benchmarking
Tracking links are essential for conducting A/B tests, where different versions of an email (e.g., different subject lines, different button colors) are sent to different segments of an audience. By comparing the click-through rates and conversion rates of each version, marketers can determine which approach is more effective. This iterative process of testing and refinement is fundamental to improving email marketing performance.
Security and Privacy Considerations
The ability to track user activity inevitably raises questions about security and privacy. Understanding how this data is handled and what safeguards are in place is crucial.
The Dual Nature of Data Collection
Tracking links collect data with the intention of improving user experience and marketing effectiveness. However, the same mechanisms could potentially be misused for more intrusive purposes if not properly managed.
Potential for Misuse and Surveillance
In the wrong hands, the data collected by tracking links could be used for unauthorized surveillance, profiling, or even malicious activities. Understanding the typical practices of reputable email service providers (ESPs) and marketing platforms is important for assessing the risk. Reputable organizations adhere to privacy regulations and best practices.
Data Anonymization and Aggregation
To mitigate privacy concerns, many organizations employ techniques like data anonymization and aggregation. Anonymization removes personally identifiable information, while aggregation combines data from multiple users to identify trends rather than individual behaviors. This helps to protect individual privacy while still allowing for valuable insights.
Your Control and Recourse
While much of this process is automatic, you are not entirely without recourse when it comes to email tracking.
Privacy Policies and Terms of Service
Reputable organizations will have clear privacy policies that outline how they collect, use, and protect your data. Reading these policies can provide clarity on their tracking practices. Understanding the terms you agree to when signing up for services or subscribing to newsletters is a proactive step.
Browser and Email Client Settings
Many browsers offer privacy settings that can limit or block certain types of tracking. Similarly, some email clients provide options to disable image loading by default, which can prevent the activation of some tracking pixels. While these measures can be effective, they might also affect the visual display of emails.
Opting Out and Unsubscribing
The most direct form of control is through opting out of communications or unsubscribing from mailing lists. This action typically signals your preference not to receive further emails, and as a result, fewer tracking links will be sent your way. It’s a fundamental right for users to manage the communications they receive.
The Future of Email Tracking and Redirects
| Aspect | Description |
|---|---|
| Email Tracking | Allows senders to monitor the delivery, open, and click-through rates of their emails. |
| Tracking Links | Special URLs embedded in emails that allow senders to track when recipients click on them. |
| Redirects | When a recipient clicks on a tracking link, they are redirected through the sender’s server before reaching the intended destination. |
| Privacy Concerns | Some recipients may be concerned about their privacy when their actions are tracked without their knowledge. |
The landscape of digital interaction is constantly evolving, and email tracking and redirects are no exception. As technology advances, so too will the methods and implications of these mechanisms.
Evolving Technologies and Techniques
The ongoing development of digital technologies will invariably impact how email tracking operates. Expect to see innovations that enhance both the efficiency of tracking and the subtlety of its implementation.
Advanced Tracking Methods
Future tracking mechanisms might involve more sophisticated browser fingerprinting techniques, AI-powered behavioral analysis, and cross-platform tracking that extends beyond email. The goal will be to gain even deeper insights into user behavior across multiple touchpoints.
The Rise of Privacy-Preserving Technologies
Conversely, there is a growing demand for privacy-preserving technologies. This could lead to the development of new encryption methods, decentralized tracking systems, and consent-based tracking models that give users more explicit control over their data. Technologies that prioritize user privacy will likely gain prominence.
The Ethical Imperative
As tracking capabilities become more potent, the ethical considerations surrounding their use will become increasingly paramount.
Transparency and User Consent
There is a clear trend towards greater transparency in data collection. Future best practices will likely emphasize obtaining explicit user consent before engaging in tracking activities. This means clear opt-in mechanisms rather than buried opt-outs.
The Balance Between Personalization and Intrusion
The challenge for marketers and service providers will be to strike a delicate balance between leveraging tracking data for personalization and avoiding intrusive surveillance. The line between helpful insights and an unwelcome invasion of privacy is a critical one to navigate. The focus will shift towards building trust through responsible data stewardship.
FAQs
1. What are email tracking links and redirects?
Email tracking links and redirects are used by email marketers and senders to track the behavior of recipients after they click on a link in an email. These links are used to gather data on open rates, click-through rates, and other engagement metrics.
2. How do email tracking links work?
When a recipient clicks on a tracking link in an email, they are redirected to a tracking server before being redirected to the intended destination. This allows the sender to collect data on the recipient’s behavior, such as the time and date of the click, the recipient’s location, and the type of device used.
3. What information is collected through email tracking links and redirects?
Email tracking links and redirects can collect a variety of information, including the recipient’s IP address, the type of device used, the email client or browser used, the time and date of the click, and the recipient’s location.
4. Are email tracking links and redirects used for malicious purposes?
While email tracking links and redirects are primarily used for marketing and analytics purposes, they can also be used for malicious activities such as phishing and malware distribution. It’s important for recipients to be cautious when clicking on links in emails from unknown or untrusted senders.
5. How can recipients protect themselves from email tracking links and redirects?
Recipients can protect themselves from email tracking links and redirects by using email clients that offer privacy and security features, such as the ability to block remote content and disable link tracking. Additionally, recipients should be cautious when clicking on links in emails and should verify the legitimacy of the sender before taking any action.









